5 Key Benefits of Infrastructure Automation
Explore the 5 key benefits of infrastructure automation, including reduced complexity, faster delivery, improved workflows, and enhanced error reduction.

The 4 Toughest Challenges to QAOps and How to Overcome Them
The QA industry is abuzz with a new term, QAOps. It integrates testing into the CI/CD pipeline and promises speed and quality. But, there are still challenges to be overcome before you see success. Here is our take on the trending practice.

The Top 5 DevOps Trends to Watch Out for in 2021
From DevSecOps to Kubernetes, here are the top 5 DevOps trends for 2021 that you need to know about.

IA, a Palindrome to AI, also means Infrastructure Agility
With new technologies disrupting the market, customer preferences evolving like never before and market dynamics changing all the time, keeping pace with change is vital.
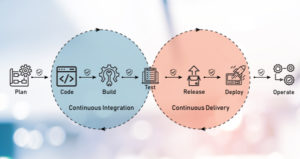
Injecting Security into CICD Pipelines
The CI/CD pipeline was built considering the speed and agility that it provided, but security was never taken into account.

An Introduction to DevSecOps
With DevSecOps, we can witness a sudden shift in the software development landscape—that of ‘shifting security left’ and making it seamlessly aligned with the development process itself to boost innovation, but securely.

Kubernetes Security: Key Factors to Consider
Here are six ways organizations can increase their Kubernetes security

Demystifying Persistent Storage Myths for Stateful Workloads in Kubernetes
Kubernetes provides workload portability. That is, any workloads should spontaneously run on any type of infrastructure where Kubernetes clusters are deployed. In the case of handling stateful workloads, it may not easy to set up persistent storage but it is not impossible

[Infoblog] DevSecOps: An Overview
DevSecOps means thinking about application and infrastructure security from the start. It also means automating some security gates to keep the DevOps workflow from slowing down. Selecting the right tools to continuously integrate security, like agreeing on an integrated development environment (IDE) with security features, can help meet these goals.

Why kubelet runs as a system service in Kubernetes cluster and not as pod/daemonsets?
Why kubelet runs as a system service in K8S cluster and not as pod/daemonsets? Many people have this question in mind when they deploy k8s cluster.
