Why the Service Mesh Will Be Essential for 5G Telecom Network
It is worth saying that service mesh technologies like Istio, Linkerd, Aspen Mesh, Consul Connect, and others play a key role in making sure better control in heterogeneous environments that have a dynamic requirement in terms of delivery.

[Infoblog] Tech Trends 2021
The digital shift arising from the pandemic is changing the way we function and has catalyzed growth for many technologies to become showstoppers. Read this article to know about the tech trends in 2021 and how Calsoft’s Mozaic offerings can help you acclimatize to the new normal.
Discover Edge Devices Intelligently with Akri in Kubernetes-Powered Edges
The Akri framework helps expose IoT devices as resources and creates services for each device in Kubernetes clusters.

Kubernetes Security: Key Factors to Consider
Here are six ways organizations can increase their Kubernetes security
Why Container Security Became A Critical Aspect For Adopters
Container security can be managed by following a few of the best practices. You can check the best practices in this HawkEye – research article. Regardless of a few vulnerabilities, containers are gravitating to its adopters not just for its speed, efficiency, and scalability but also for its self-contained security model.

Evolution Of Data Centers
Clubbing of individual components of a Datacenter to form a single node is called a Converged Infrastructure. Clubbing of Software-Defined components to form a node is called Hyper-Converged Infrastructure. The next era is going to be the era of Hybrid Infrastructure where few components will be hardware-based and few will be software-based.
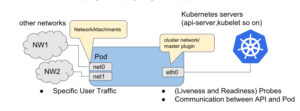
A Primer on Multus-CNI
This blog is for those who are looking forward to getting started with Multus CNI, the blog covers an overview of CNI in Kubernetes, Multus CNI plugin, basic configuration along with a quick deployment scenario.

VMware Project Pacific – Technical Overview
This project is Open source has a lot of potentials to improve, custom CRDs and Controllers can be written to integrate new tools and stacks into the vSphere infrastructure as an instance creating a MongoDB CRD, controller that can deploy a MongoDB instance by just specifying the details in the manifest and the controller can then keep a watch on the desired state.
[Infoblog] Kubernetes for Storage
Kubernetes for storage is useful for storage administrator because it enables different forms of persistent, stateful data retention within Kubernetes clusters deployment, which are increasingly popular.

Demystifying Persistent Storage Myths for Stateful Workloads in Kubernetes
Kubernetes provides workload portability. That is, any workloads should spontaneously run on any type of infrastructure where Kubernetes clusters are deployed. In the case of handling stateful workloads, it may not easy to set up persistent storage but it is not impossible
